Today we’re delighted to publish our report, ‘NIST security vulnerability trends in 2020: an analysis’.
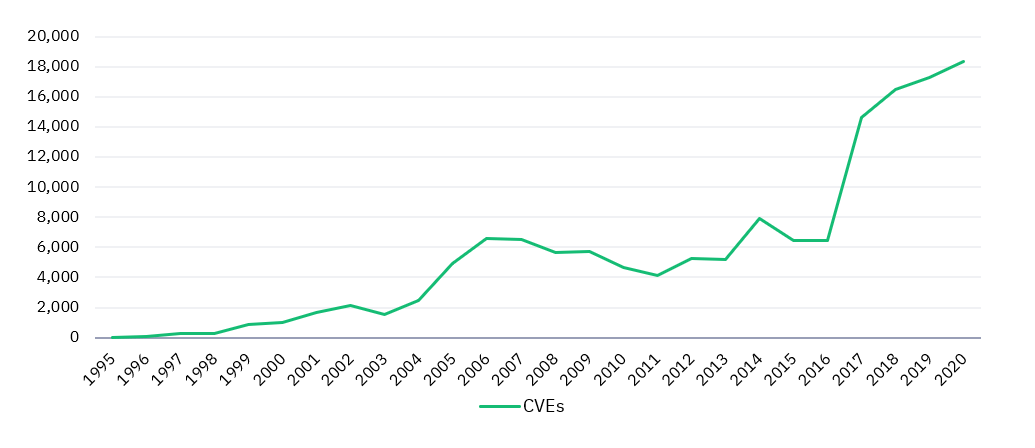
The report is based on an analysis of more than 18,000 Common Vulnerabilities and Exposures (CVEs) logged to NIST’s National Vulnerability Database in 2020. It reveals that well over half (57%) were rated ‘high’ or ‘critical’ severity – the highest recorded figure for any year to date.
Our analysis also looks beyond severity scores, detailing the rise of low complexity vulnerabilities as well as those which require no user interaction to exploit.
These trends highlight the need for organisations to improve their understanding of the vulnerabilities actively exploited in the wild, as well as to adopt a multi-layered approach to vulnerability management.
The findings aren’t all bad news. There are also positive trends, such as a decrease in CVEs which require no privileges to exploit.
An insight into changing CVE trends
NIST is the US National Institute of Standards and Technology, and its National Vulnerability Database (NVD) is a repository of Common Vulnerabilities and Exposures (CVEs) one of the most trusted sources of information for IT and security professionals around the world.
Our report focuses on vulnerabilities added to the NVD in 2020, examines wider CVE trends since 1989 and also offers security advice to organisations.
Key findings include:
- More security vulnerabilities were disclosed in 2020 (18,103) than in any other year to date – at an average rate of 50 CVEs per day
- 57% of vulnerabilities in 2020 were classified as being ‘critical’ or ‘high’ severity (10,342)
- Low complexity CVEs are on the rise, representing 63% of vulnerabilities disclosed in 2020
- Vulnerabilities which require no user interaction to exploit are also increasing, representing 68% of all CVEs recorded in 2020
- Vulnerabilities which require no user privileges to exploit are on the decline (from 71% in 2016 to 58% in 2020)
“Analysis of the NIST NVD presents a mixed outlook for security teams,” comments George Glass, Head of Threat Intelligence at Redscan.
“Vulnerabilities are on the rise, including some of the most dangerous variants. However, we’re seeing more positive signs, including a drop in the percentage of vulnerabilities which require no user privileges to exploit.”
“Vulnerabilities are on the rise, including some of the most dangerous variants. However, we’re seeing more positive signs, including a drop in the percentage of vulnerabilities which require no user privileges to exploit.”
George Glass, Head of Threat Intelligence at Redscan
CVEs recorded by NIST NVD (1995-2020)
Vulnerability management advice for security teams
Among the recommendations of the new NIST report is that cyber security professionals should draw upon the latest threat intelligence data to improve vulnerability management. George adds:
“When analysing the potential risk that vulnerabilities pose, organisations must consider more than just CVE severity score. Many CVEs are never or rarely exploited in the real world because they are too complex or require attackers to have access to high level privileges.
“Identifying which vulnerabilities to prioritise is a perennial challenge in IT security, especially as the number of CVEs only continues to grow. To aid decision-making, security teams need a practical understanding of the potential impact vulnerabilities pose and how readily they are being exploited in the wild.”
“Identifying which vulnerabilities to prioritise is a perennial challenge in IT security, especially as the number of CVEs only continues to grow. To aid decision-making, security teams need a practical understanding of the potential impact vulnerabilities pose and how readily they are being exploited in the wild.”
George Glass, Head of Threat Intelligence at Redscan
Download the report to learn about the steps your organisation can take to enhance vulnerability management in 2021.
If you want to read more about this report, check out some of our recent media coverage:




