Kroll’s Q4 2021 Threat Landscape report reveals that many of the biggest security challenges of the past year look likely to continue through 2022, with ransomware remaining the most common attack type.
Created by threat intelligence specialists from Kroll and Redscan, the new report, Q4 2021 Threat Landscape: Software Exploits Abound, explores key insights and trends from over 3,000 cyber incidents handled worldwide in 2021.
In early December 2021, Redscan’s analysis of the National Vulnerability Database (NVD), the Common Vulnerability Database (CVD) repository of the U.S. National Institute of Standards and Technology, revealed that 2021 officially broke the record for common vulnerabilities and exposures (CVEs) logged by researchers.
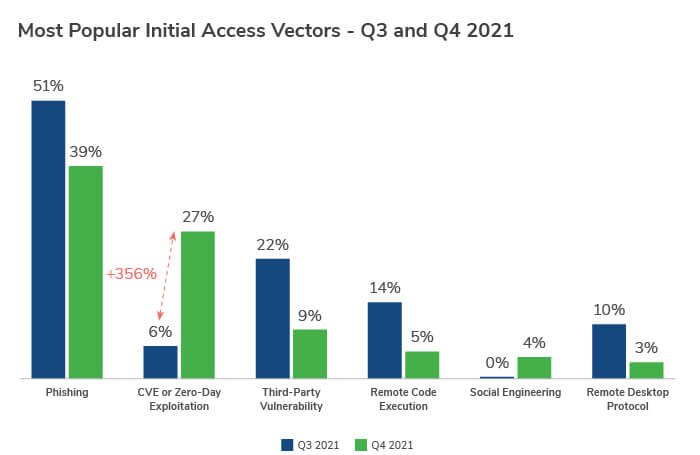
This new report outlines how cyber vulnerabilities continue to be exploited at great speed, with Kroll identifying a 356% growth in the number of incidents where zero-days or freshly-announced vulnerabilities were the initial infection vector, compared to Q3 2021.
This underscores the risk to organisations in the wake of high-profile vulnerability notifications – and the speed with which cybercriminals are able to exploit weaknesses in companies’ defences.
The report also discusses:
- The most prominent attack methods of 2021 and how they have changed in recent months
- The statistics that make the professional services sector the most targeted sector in Q4
- The vulnerabilities most popular with ransomware actors, including how Log4Shell is being used to gain initial access to organisations’ networks
- How adversaries are leveraging Exchange vulnerabilities (tied to ProxyLogon and ProxyShell) to conduct new attacks, even after servers have been fully patched
What organisations need to do to stay ahead of evolving threats
As the report confirms, it is essential to remain vigilant and ready to respond to the continued acceleration of cyber threats throughout 2022. The report’s findings highlight the importance of harnessing threat intelligence and having an effective Managed Detection and Response program in place to enable threat validation and containment and support post-incident recovery.




