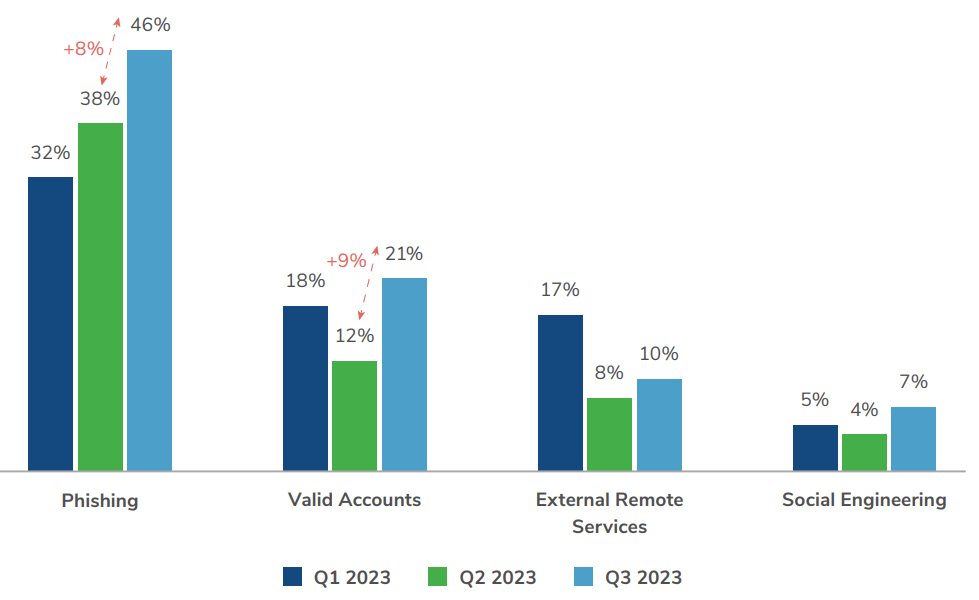
Kroll’s latest threat landscape report reveals a dramatic escalation of social engineering tactics.
This rise in social engineering was seen alongside significant increases in phishing, smishing, vishing, the use of valid accounts and other tactics – adding up to the highest volume of incidents seen in 2023.
These, as well as other notable trends from the previous quarter, are discussed in the report, Q3 2023 Threat Landscape Report: Social Engineering Takes Center Stage.
Human hacking evolves
Q3 2023 saw social engineering, also known as ‘human hacking’, evolve from a long-standing security challenge to threat actors’ method of choice. The increasing volume of social engineering attacks is matched by a broadening range of approaches. As part of the rise in social engineering, business email compromise (BEC) continues to grow steadily in popularity, with both established and newer threat actor groups using a range of tactics to access data and, in some cases, ransom the information.
The rise in social engineering activity aligns with multiple open-source reports warning about these types of attacks via Microsoft Teams and the rise of activity by the group KTA243 (SCATTERED SPIDER), which uses phone- and SMS-based social engineering tactics to lure users into exposing their credentials.
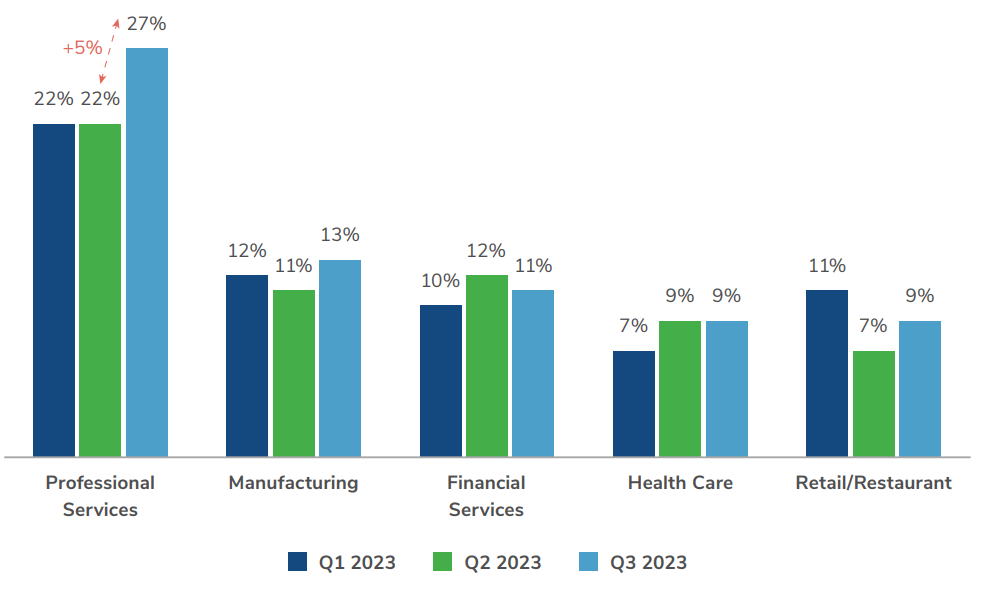
Professional services stay in the spotlight
In Q3, Kroll continued to see the professional services sector rank first across cases. Similarly to Q1, Kroll saw a high concentration of this activity related to legal firms, fuelled by a rise in BEC across all sectors and specific campaigns targeting the legal industry, such as the BLACKCAT ransomware gang.
Kroll also observed nominal rises in the targeting of the manufacturing (2%) and construction sectors (1.5%) from the previous quarter. For manufacturing, ransomware was the second most likely threat type to be observed, while insider threat was the second most likely threat type for construction.
Threat incident types
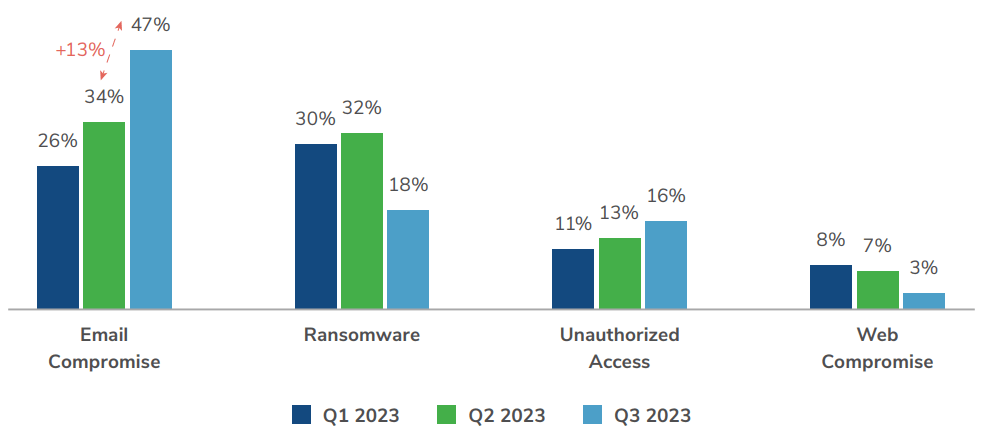
BEC continues to increase steadily in popularity. According to the latest Internet Crime Report from the FBI’s Internet Crime Complaint Center (IC3), businesses lost more than $2.7 billion due to BEC. In Q3, Kroll saw an uptick in events related to email compromise, fuelling that threat to account for nearly 47% of cases during the quarter.
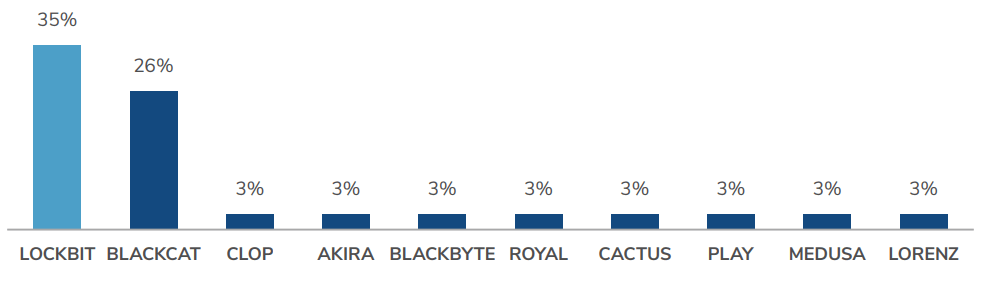
Ransomware variants – Q3 2023
Despite BEC taking centre stage, ransomware remains an ever-present threat. While the total percentage of ransomware cases dropped in Q3 (-13.5%), the number of individual ransomware engagements was consistent with previous quarters. The most active groups observed in Q3 were LOCKBIT and BLACKCAT. Kroll also saw increases in activity around newer groups such as CACTUS, RHYSIDA and INC.
As shown in other recent Kroll analysis, organisations are not only at risk from evolving threats but also from their own perception of their readiness to address those threats. By working with a trusted and field-proven security partner, businesses can ensure they are prepared to respond effectively to the challenges that lie ahead. Working toward true cyber maturity will ensure that organisations are better equipped to defend both against novel security challenges and the resurgence and reinvention of familiar threats.